Cybersecurity threats are a constant concern for organizations across all sectors. The ability to detect and respond to these threats swiftly can make the difference between a minor incident and a major breach. A single vulnerability in a security framework can lead to significant data loss, operational downtime, and compromised sensitive information.
Operation centers equipped with advanced video wall solutions help to provide full visibility over your business activities. This enhanced visibility ensures that potential threats are detected quickly, allowing for immediate action and minimal downtime. By integrating robust monitoring protocols and utilizing cutting-edge technology, operation centers are essential in maintaining the integrity and security of your organization’s critical data and systems.
Learn more about how we help Legato Security standardize their SOC here.
This blog will explore the pivotal role that operation centers play in minimizing cybersecurity threats and breaches thanks to advanced monitoring and control over your video wall content.
What’s Content Are You Displaying on Your Video Wall?
Operation centers, leveraged by organizations such as enterprises, public safety, security operations, and critical infrastructure facilities, typically use video wall displays to monitor their cybersecurity status and view real-time data to ensure smooth operational performance. By providing real-time visibility and management of sensitive data, the content displayed on your video wall and the ease of control and visibility are imperative for safeguarding against disruptions and mitigating the impact of cyber incidents.
What you can monitor:
- Security camera footage
- Network traffic data
- Access logs and user activity
- Incident reports and response
- Confidential business information
- Endpoint security
- Application security
- Threat intelligence
- Potential vulnerabilities
- Data Loss Prevention (DLP) tools
By continuously monitoring these critical areas, cybersecurity operation centers provide a comprehensive defense against cyber threats, ensuring the resilience and security of an organization’s operations. The integration of advanced video wall solutions in your operation center enhances these capabilities by providing a unified view of all monitoring activities, enabling quicker detection and response to threats.
The Importance of User Access and Control
Knowing who has access to what information is paramount in operation centers. It is critical to cybersecurity that systems are protected against unauthorized personnel who could manipulate data or disrupt critical operations. As a result, identity management and access control are foundational elements of a robust cybersecurity strategy – as well as video wall system components.
More specifically, it’s important that your video wall solution is set up to support granular access control. Administrators can define user roles and permissions with precision, ensuring only authorized personnel can access sensitive data displayed on the video wall. Also, users have the appropriate level of access to fulfill their specific responsibilities. By having different levels of user control, you can help streamline what each user needs to monitor, clearing out the extra clutter on your video wall display.
See how easy it is to manage your access points with
Haivision Command 360
Haivision Command 360 for Your Cybersecurity-Critical Workflows
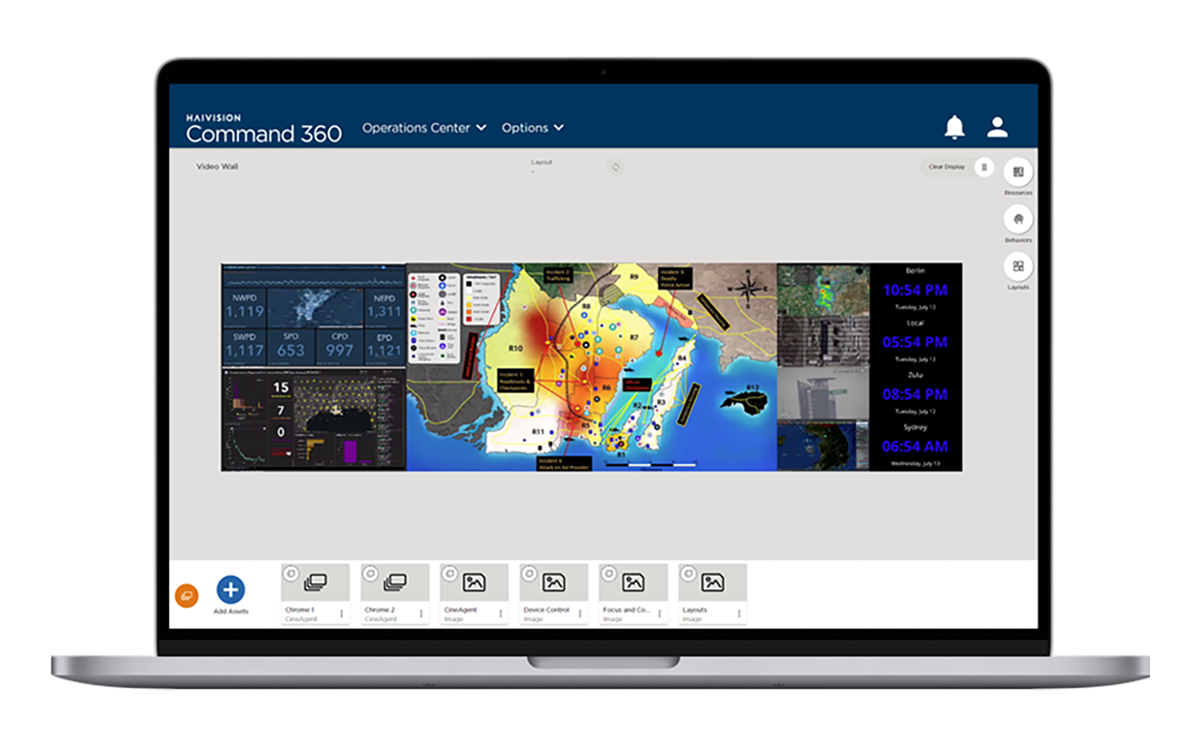
We understand that you have critical workflows and complex infrastructures. Our video wall solution, Haivision Command 360 ensures that you have full visibility over your operations so when an attack or breach occurs, you’re able to detect and identify the problem quickly, and implement the right procedures with minimal disruption.
Haivision Command 360, was designed to support operations that require constant monitoring. It provides a multi-layer approach by supporting your existing cybersecurity frameworks and ensuring the visibility necessary to monitor all your operations in real-time, all in a single location.
Detailed user access controls allow administrators to define permissions for individual users or groups. This ensures that only authorized personnel have access to sensitive information displayed on the video wall.
Command 360 also provides a comprehensive view of multiple sources so that teams can monitor all mission-critical systems. With a holistic view of real-time data, security teams can track user activity, identify potential threats, and take immediate action to mitigate any suspicious behavior. These real-time insights empower proactive security management for your operation center.
Secure your Operations with Our Complete Video Wall Solution
With a deep understanding of security, Haivision designed Command 360 with robust features that support cybersecurity operations. By integrating seamlessly with existing security frameworks, offering granular user access control, and leveraging industry-standard encryption, Command 360 empowers cybersecurity operation centers to operate with confidence.
Command 360 incorporates features that align with Zero Trust principles, such as multi-factor authentication and least-privilege access. This layered approach helps mitigate the risks associated with accidental errors or more malicious actions, like social engineering attacks and stolen credentials. Lastly, Haivision video wall solution offers real-time monitoring capabilities, allowing security teams to identify and address suspicious activity promptly. With sophisticated cyberattacks on the rise, proactive threat detection is critical for secure environments.