For IT professionals, the terms SOC and NOC are familiar, but for those new to the field, understanding the distinctions and synergies between security operations centers (SOCs) and network operations centers (NOCs) is essential. Today, these environments rarely operate independently. They’re critical to defense agencies, government organizations, space programs, utilities, financial institutions, and technology enterprises, helping manage and protect increasingly complex, distributed, and high-stakes digital (and physical) infrastructures.
As video volumes grow, cyber threats evolve, and operational decisions must be made in real time, SOCs and NOCs are increasingly expected to operate from shared context rather than separate silos. In this blog post, we will explore the evolving roles of SOCs and NOCs, how they intersect across industries and how video wall solutions like Haivision Command 360 support a unified operational view across cybersecurity, network performance, and mission-critical workflows.
Defining the Roles of SOCs and NOCs
First, let’s establish the fundamentals, including the key responsibilities and functions of each type of center.
A security operations center (SOC) is the digital guardian of your organization. Think of it as the security hub, responsible for identifying, analyzing, and mitigating cybersecurity threats. In essence, the SOC is your shield against cyberattacks. Modern SOCs operate in real time, correlating alerts, telemetry, and video feeds to assess risk and guide rapid response. Whether protecting mission data or securing banking transactions, SOCs help detect malicious activity, coordinate responses, and ensure compliance with industry regulations, financial interests, and government and defense standards.
On the other hand, a network operations center (NOC) is the central nervous system of your IT infrastructure. NOCs focus on ensuring network performance, availability, and managing network incidents. Beyond uptime alone, today’s NOCs are responsible for understanding how performance issues impact critical services and downstream operations. In sectors like energy and utilities, finance, or technology, NOCs monitor grid performance, secure interconnection flows, and enable 24/7 uptime for critical services.
While SOCs focus on cybersecurity and NOCs focus on network performance, both contribute to the same goal: maintaining situational awareness and ensuring operational continuity across the organization.
The Synergy Between SOCs and NOCs
In many organizations, the distinction between SOC and NOC can be blurry, and increasingly, that overlap is intentional. SOCs often collaborate with NOCs, sharing critical information about network threats and incidents. This collaboration is vital because a network issue can sometimes be the result of a security breach, and vice versa. In the utilities sector, compromised network performance might point to a broader cyber threat to operational technology (OT) systems, whereas in a space command center, NOC and SOC teams must work in tandem to maintain secure telemetry, video feeds, and communications during launches or satellite operations. The key is not simply communication, but access to a shared operational picture that enables coordinated, confident decision-making.
Addressing the misconception of redundancy is crucial. While there is some overlap in incident response, both SOCs and NOCs serve different primary functions, and alignment between the two improves speed, accuracy, and resilience during critical events.
Tools and Technologies
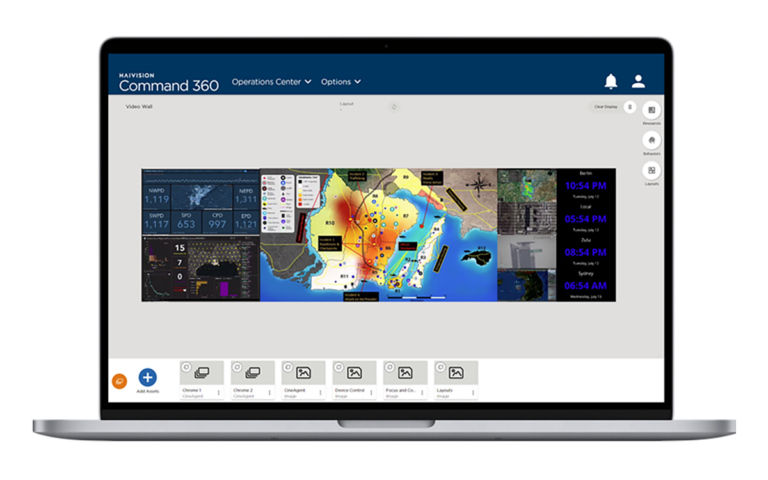
One of the technologies that has gained prominence in both SOCs and NOCs is Haivision Command 360, our complete video wall solution. This innovative solution allows operators to have a real-time, panoramic view of the network and security status all in one common operating picture, enhancing situational awareness and helping operators coordinate faster and more effectively.
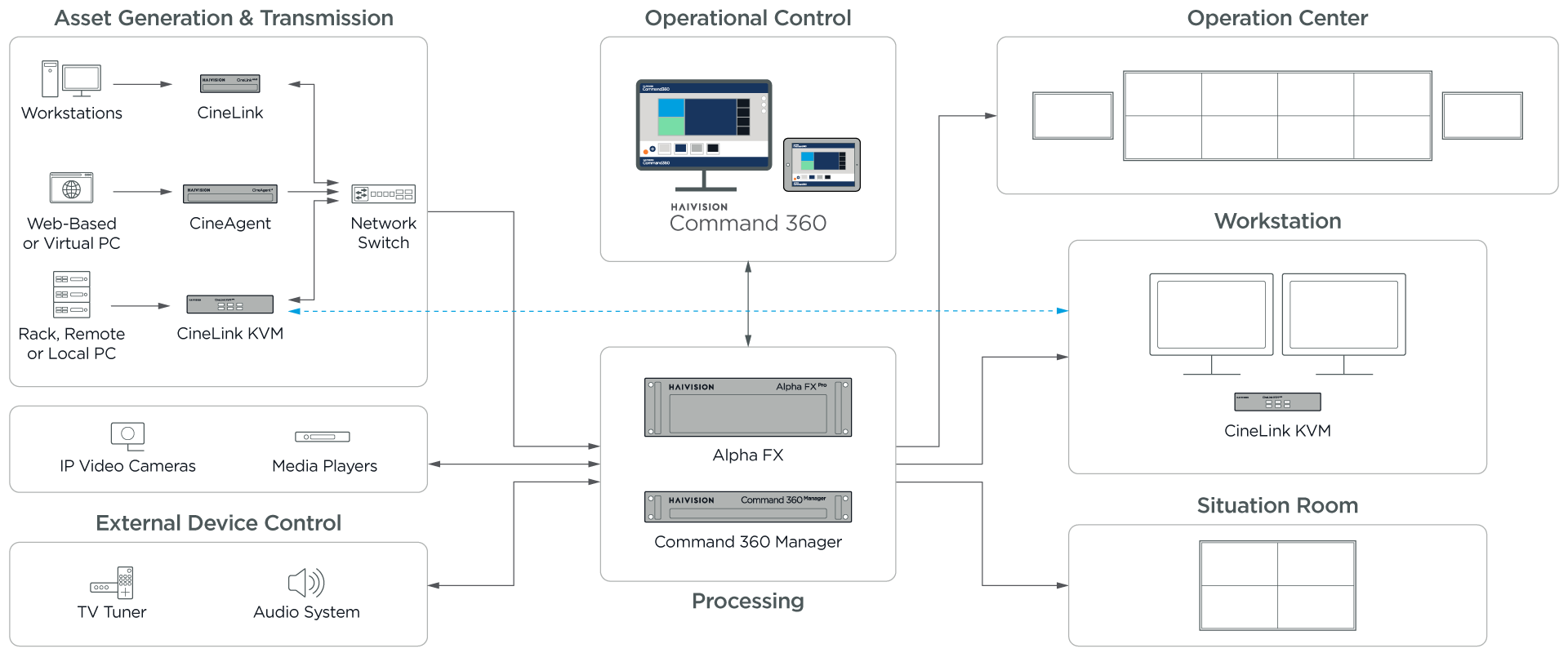
Common tools and technologies used in SOCs include Security Information and Event Management (SIEM) tools, intrusion detection systems, and antivirus software. NOCs, on the other hand, rely on network monitoring and management tools, such as network performance monitoring systems, telemetry visualization (critical for space and defense), traffic and flow analyzers, and OT/IT monitoring tools (especially in energy and utilities). Rather than replacing these systems, Command 360 works alongside them, visually unifying outputs from multiple tools into a coherent operational view.
Industry-Specific Considerations
Different industries emphasize SOC and NOC functions in distinct ways:
- Government: Protecting critical government networks and citizen data across federal, state, and municipal agencies
- Technology: Managing uptime and performance of global SaaS and cloud platforms
- Energy and Utilities: Integrating OT/IT to ensure grid stability and secure energy generation
- Finance and Banking: Detecting fraud, securing payment networks, and ensuring always-on availability for transactions
- Military and Defense: Securing classified data, managing ISR video feeds, maintaining global communications
Skills and Expertise Required
While the skills needed for personnel in a SOC or a NOC can vary, the solution itself needn’t require highly technical abilities. For optimal effectiveness, these types of operation centers must rely on easy-to-use infrastructure because operators need their focus directed solely on critical events as they unfold. It’s in these circumstances that cumbersome technology can slow down critical response time.
Haivision Command 360 was designed for technical and non-technical users alike, eliminating a layer of complications. Ultimately, it’s Haivision’s goal to allow technology to supercharge an organization’s visualization capabilities by way of easy-to-use software.
Operational Challenges
Both SOCs and NOCs face operational challenges, including coordination issues. To overcome these challenges, organizations need to foster a culture of collaboration, ensuring that critical information flows seamlessly between operators. Establishing clear communication protocols and regular joint training exercises can help bridge the gap.
Future Trends
As technology continues to evolve, we expect SOC and NOC operations to follow suit. Automation and artificial intelligence are playing an increasingly significant role in threat detection and incident response, translating, most likely, to increased efficiency and effectiveness. The impact of remote work on these operations is also noteworthy, as it requires a shift in strategies and tools to secure a dispersed workforce. Embracing these trends will be crucial for organizations looking to stay ahead in cybersecurity and network performance.
The need for businesses to invest in SOC or NOC capabilities is undeniable. These centers have become essential across industries for IT, cybersecurity, critical infrastructure protection, and financial stability applications, ensuring the health, security, and performance of an organization’s digital infrastructure.
As security and network operations become more interconnected and time-sensitive, flexible operation center technologies like Haivision Command 360 help organizations scale, align teams, and make faster, more confident decisions when it matters most.
Haivision Command 360
Transform your operations with Haivision Command 360: the complete video wall solution for operation and command centers.

